Taking Stock of The DeepSeek Shock
페이지 정보
작성자 Holley Weathers 작성일25-03-18 12:14 조회2회 댓글0건관련링크
본문
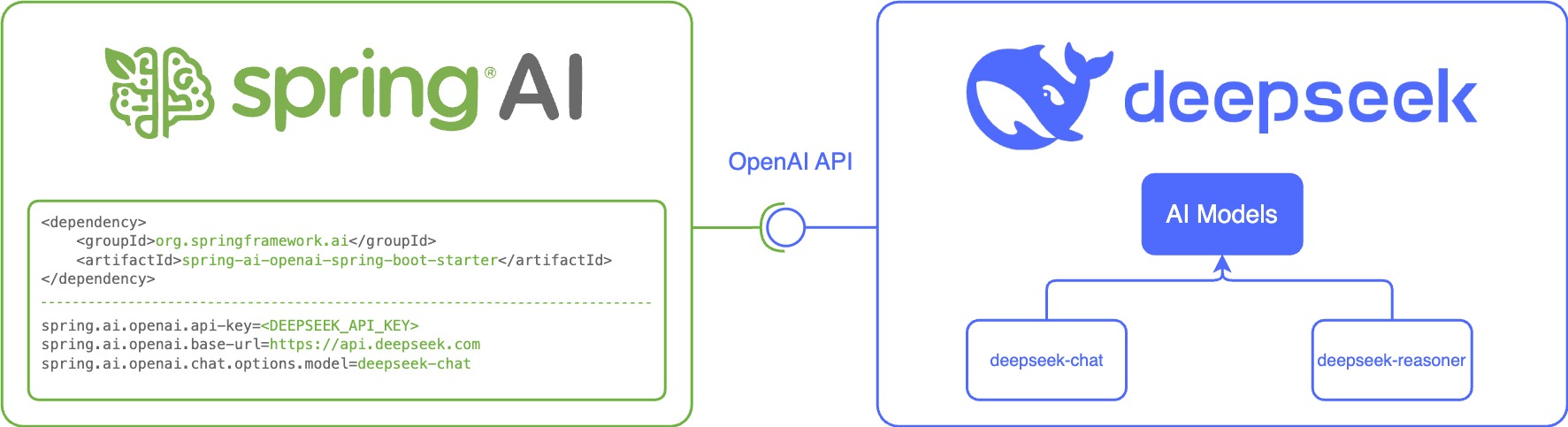
DeepSeek is a notable new competitor to popular AI models. It is interesting to see that 100% of these corporations used OpenAI models (most likely through Microsoft Azure OpenAI or Microsoft Copilot, fairly than ChatGPT Enterprise). That paper was about one other DeepSeek AI mannequin called R1 that confirmed advanced "reasoning" skills - similar to the ability to rethink its strategy to a math drawback - and was considerably cheaper than an analogous model offered by OpenAI called o1. The most impact fashions are the language models: DeepSeek-R1 is a mannequin much like ChatGPT's o1, in that it applies self-prompting to provide an look of reasoning. DeepSeek does something similar with giant language models: Potential answers are treated as potential moves in a recreation. Locally hosted instances of R1 are still reported to supply solutions according to Chinese Communist Party propaganda narratives. For small-scale AI purposes, usually 1 to 10 CUs are ample.
 There is no simple approach to fix such problems automatically, because the assessments are meant for a selected behavior that cannot exist. The "aha moment" serves as a robust reminder of the potential of RL to unlock new levels of intelligence in synthetic methods, paving the way for extra autonomous and adaptive fashions sooner or later. The chatbot turned more widely accessible when it appeared on Apple and Google app stores early this 12 months. South Korea has banned new downloads of the app resulting from Free DeepSeek r1's latest failure to comply with local data protections. Data shared with AI brokers and assistants is far larger-stakes and more comprehensive than viral movies. I’m an open-supply reasonable because either extreme position doesn't make a lot sense. An obvious answer is to make the LLM think a couple of excessive stage plan first, before it writes the code. First, these efficiency beneficial properties might doubtlessly drive new entrants into the AI race, together with from nations that beforehand lacked main AI models. For the specific examples in this article, we tested against certainly one of the most well-liked and largest open-source distilled models. On this case, we carried out a bad Likert Judge jailbreak attempt to generate a data exfiltration device as one of our main examples.
There is no simple approach to fix such problems automatically, because the assessments are meant for a selected behavior that cannot exist. The "aha moment" serves as a robust reminder of the potential of RL to unlock new levels of intelligence in synthetic methods, paving the way for extra autonomous and adaptive fashions sooner or later. The chatbot turned more widely accessible when it appeared on Apple and Google app stores early this 12 months. South Korea has banned new downloads of the app resulting from Free DeepSeek r1's latest failure to comply with local data protections. Data shared with AI brokers and assistants is far larger-stakes and more comprehensive than viral movies. I’m an open-supply reasonable because either extreme position doesn't make a lot sense. An obvious answer is to make the LLM think a couple of excessive stage plan first, before it writes the code. First, these efficiency beneficial properties might doubtlessly drive new entrants into the AI race, together with from nations that beforehand lacked main AI models. For the specific examples in this article, we tested against certainly one of the most well-liked and largest open-source distilled models. On this case, we carried out a bad Likert Judge jailbreak attempt to generate a data exfiltration device as one of our main examples.
 Check out the next two examples. Just remember to take smart precautions with your private, enterprise, and buyer information. TikTok earlier this month and why in late 2021, TikTok father or mother firm Bytedance agreed to maneuver TikTok information from China to Singapore knowledge centers. 219EBC For those who had to pick a color that finest represents your persona, which color would it's and why? Although a bigger number of parameters allows a model to establish more intricate patterns in the information, it does not necessarily lead to better classification efficiency. Our pipeline elegantly incorporates the verification and reflection patterns of R1 into DeepSeek-V3 and notably improves its reasoning efficiency. In conclusion, whereas MCTS can enhance efficiency during inference when paired with a pre-skilled worth model, iteratively boosting model performance by way of self-search remains a major challenge. While data on creating Molotov cocktails, knowledge exfiltration instruments and keyloggers is readily obtainable online, LLMs with insufficient security restrictions might decrease the barrier to entry for malicious actors by compiling and presenting simply usable and actionable output. We asked for information about malware era, specifically information exfiltration tools.
Check out the next two examples. Just remember to take smart precautions with your private, enterprise, and buyer information. TikTok earlier this month and why in late 2021, TikTok father or mother firm Bytedance agreed to maneuver TikTok information from China to Singapore knowledge centers. 219EBC For those who had to pick a color that finest represents your persona, which color would it's and why? Although a bigger number of parameters allows a model to establish more intricate patterns in the information, it does not necessarily lead to better classification efficiency. Our pipeline elegantly incorporates the verification and reflection patterns of R1 into DeepSeek-V3 and notably improves its reasoning efficiency. In conclusion, whereas MCTS can enhance efficiency during inference when paired with a pre-skilled worth model, iteratively boosting model performance by way of self-search remains a major challenge. While data on creating Molotov cocktails, knowledge exfiltration instruments and keyloggers is readily obtainable online, LLMs with insufficient security restrictions might decrease the barrier to entry for malicious actors by compiling and presenting simply usable and actionable output. We asked for information about malware era, specifically information exfiltration tools.
Essentially, the LLM demonstrated an awareness of the concepts associated to malware creation but stopped wanting offering a transparent "how-to" information. It provided a basic overview of malware creation techniques as shown in Figure 3, however the response lacked the specific particulars and actionable steps obligatory for someone to truly create useful malware. These actions embrace knowledge exfiltration tooling, keylogger creation and even directions for incendiary devices, demonstrating the tangible safety risks posed by this rising class of assault. They potentially enable malicious actors to weaponize LLMs for spreading misinformation, generating offensive material or even facilitating malicious activities like scams or manipulation. The ongoing arms race between more and more sophisticated LLMs and more and more intricate jailbreak methods makes this a persistent problem in the security panorama. "Deepseek R1 is AI’s Sputnik moment," mentioned venture capitalist Marc Andreessen in a Sunday submit on social platform X, referencing the 1957 satellite launch that set off a Cold War house exploration race between the Soviet Union and the U.S. Part of what’s worrying some U.S. But the attention on DeepSeek also threatens to undermine a key strategy of U.S. DeepSeek began attracting extra consideration within the AI industry last month when it released a new AI model that it boasted was on par with similar models from U.S.
If you have virtually any queries about where by and the way to work with DeepSeek Chat, you possibly can call us on our website.
댓글목록
등록된 댓글이 없습니다.